Dear Readers,
The faster we build with AI, the more we break, and Aikido Security co-founder Roeland Delrue has a front-row seat to the chaos.
In today's featured interview, he reveals how "vibe coding" is letting developers ship three to four times faster while flooding codebases with vulnerabilities that no human team can keep up with, and why autonomous AI agents that pen-test, patch, and retest around the clock might be the only answer.

But the security of code is just one pressure point in a week full of collisions between ambition and reality: an EpochAI deep dive shows that the Iran conflict could quietly reshape AI economics by squeezing helium, energy, and Gulf investment flows, a single round of CAR-T cell therapy sent a woman with three autoimmune diseases into full remission, hinting at a medical paradigm shift, and new data reveals that nearly half of Gen Z workers are actively sabotaging AI rollouts at their companies, even as those who embrace the tools pull dramatically ahead in pay and promotions.
Whether you're shipping code, building infrastructure, or just trying to keep your job in a world that's rewriting itself weekly, today's issue has something that will make you rethink what's coming next.
All the best,

Kim Isenberg

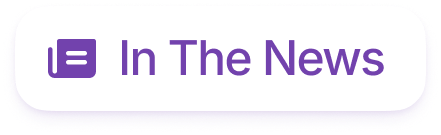
🔥 Iran War Reshapes AI Economics
EpochAI report: A prolonged Hormuz disruption is unlikely to derail AI progress, but it could slow data center expansion and strain energy and helium supply chains, especially in Europe and Asia. Crucially, the biggest impact may come from reduced Gulf investment flows, though major players like U.S. tech giants remain financially dominant; honestly, this is more resilient than many would expect.
Overall, AI’s core engine - chip production and compute scaling - looks durable unless the conflict escalates dramatically, but second-order economic shocks could still ripple through the industry.

🧬 Immune Reset Drives Stunning Remission
A 47-year-old woman with three severe autoimmune diseases achieved complete, treatment-free remission after a single round of CAR-T cell therapy, which effectively “reset” her immune system by eliminating malfunctioning B cells. Within weeks, her symptoms vanished, blood markers normalized, and she no longer needed daily transfusions. This is more impactful than expected for such complex conditions.
Nearly a year later, her immune system rebuilt itself with “naive” cells that no longer attack her body, hinting at a breakthrough approach that could transform treatment for autoimmune diseases, though larger trials are still needed.

🤖 Gen Z Quietly Fights AI
A surprising 29% of employees - and 44% of Gen Z - admit sabotaging AI rollouts, driven largely by fear of job loss (“FOBO”) and distrust of the technology. Some are refusing tools, manipulating outputs, or even skewing performance data to make AI look ineffective, yet ironically, 60% of executives are considering layoffs for those resisting AI adoption.
Meanwhile, workers who embrace AI are pulling ahead fast - “super-users” are 3× more likely to get raises and promotions and save nearly 9 hours per week, showing that resisting AI may actually accelerate the very outcome workers fear. Honestly, this is more impactful than expected, adaptation, not resistance, is becoming the real job security.


88% resolved. 22% loyal. Your stack has a problem.
Those numbers aren't a CX issue — they're a design issue. Gladly's 2026 Customer Expectations Report breaks down exactly where AI-powered service loses customers, and what the architecture of loyalty-driven CX actually looks like.


Democratizing Cybersecurity In The AI Era
“I think a lot of these cyber products out there, they're like F-35 fighter jets:
they can do all kinds of maneuvers, but you need three months of training to understand what's going on.”
The Takeaway
👉 The AI Code Bottleneck: The rapid adoption of "vibe coding" allows developers to produce code three to four times faster, but it simultaneously introduces a massive surge in complex security vulnerabilities and expands the attack surface.
👉 Self-Securing Software: To keep pace, the industry is shifting from slow, manual yearly audits to autonomous AI agents that continuously run penetration tests, validate threats, and automatically write fixes.
👉 Humans as Orchestrators: As AI takes over the mundane tasks of writing and checking code, the role of developers—and even non-technical staff—will evolve into "orchestrators" who guide and manage these automated agentic workflows.
👉 Democratization vs. Sovereignty: A major trend shaping the future of tech is the clash between two opposing forces: the massive democratization of software creation/security and the growing global push for strict data sovereignty.

(Aikido team)
Aikido is one of Europe's fastest-rising cybersecurity startups. Today we explore why AI code is the new bottleneck.
Kim Isenberg: Hi, I'm Kim Isenberg, Superintelligence Editor in Chief. Today I'm excited to welcome Roeland Delrue, co-founder of Aikido Security. Roeland, it's a pleasure to meet you. Why don't you tell us a bit about yourself?
Roeland Delrue: Thanks for having me. I'm the commercial co-founder of Aikido. In practice, I talk a lot with customers and partners. We do software security across the entire software development lifecycle—from the moment code gets written, whether by humans, AI, or a hybrid, all the way to the apps being live. It used to be a long cycle, but with "vibe coding," it has quickened a lot.
Kim Isenberg: Aikido is one of Europe's fastest-rising cybersecurity startups. Why do you believe software security is becoming the new bottleneck in the age of AI-generated code?
Roeland Delrue: Like every powerful technology, there's always a threat and an opportunity at the same time. The sheer embracement of Generative AI for code generation has been incredible. Developers are producing code three to four times faster. We can actually see it in our statistics because we scan code: companies are producing a lot more, and the PRs (Pull Requests) are often a little bit more bloated and complex. It introduces new attack vectors. Cybersecurity has always been a cat-and-mouse game, but to keep up right now, it's a little bit like fighting fire with fire. The sheer speed and complexity have taken a couple of levels up in the last year.
Kim Isenberg: What exactly changed over the last 12 to 18 months that makes this problem feel so urgent right now?
Roeland Delrue: The products and the models have gotten a lot better. I remember sitting next to developers back when we were a smaller startup; they would prompt ChatGPT, double-check it, and maybe copy-paste something. Now, IDEs have embraced this, the UX has improved, and the quality of the models is night and day compared to a year ago. It has reached that critical point where people start to blindly trust it, and it's getting closer to autopilot.
Kim Isenberg: You founded the company in Ghent, not in Silicon Valley. What made you believe a European team could compete here, and what problem are you actually trying to solve?
Roeland Delrue: We were really just scratching our own itch. Before Aikido, we spent 12 years building FinTech and HR apps that hold sensitive data. Our customers expected us to be secure, so we were in the market for code scanners, cloud scanners, static testers, and dynamic testers. It was not fun. They were enterprise-focused, caused "sticker shock" because they hid their pricing, and honestly, they were hard to use. They would literally make you feel dumb, like you needed a PhD in cybersecurity. I think a lot of these cyber products out there are like F-35 fighter jets: they can do all kinds of maneuvers, but you need three months of training to understand what's going on. We felt we could democratize security by combining different scanners, taking out the false positives, and making it user-friendly.
Kim Isenberg: You use the term "self-securing software." What does that mean in simple terms?
Roeland Delrue: It means letting AI agents take over. In the real world, we're moving towards robots that will water our plants and pick up our mail. In security, we traditionally had one manual penetration test a year, resulting in a PDF report. But that's too late. We built agentic versions that run continuous pen tests. Agents never sleep, don't go on holiday, and can be indefinitely scaled. But it doesn't stop at finding issues. We also have remediation agents that fix the vulnerabilities, and retest agents that try to hack the new fixes. They are continuously roaming the application, finding and fixing issues on a never-ending journey.
Kim Isenberg: The more code is generated, the more demand there is for cybersecurity. Are we seeing a massive increase in vulnerabilities?
Roeland Delrue: Yes. The number of CVEs (Common Vulnerabilities and Exposures) is an upward graph. At Aikido, we scan 15 different open-source ecosystems, like NPM and PyPI, for malware to prevent supply chain attacks. Last year, we were scanning about 30,000 packages a day. Now it's 100,000. The sheer amount of open-source software the world is publishing is ever-increasing, and we have to keep up.
Kim Isenberg: Could you walk us through a very concrete example of how a customer uses Aikido in practice?
Roeland Delrue: Typically, they start with a full "white box" pen test. We unleash hundreds of agents that map out the codebase and attack the application. That full test forms the baseline. From then on, every time they ship a new release, a mini pen test runs automatically. In the old world, traditional scanners had a terrible signal-to-noise ratio—they might find 400 things, but only 5% are real. Our agents bring static and dynamic testing together. If they see something in the code, they immediately try to exploit it dynamically. Instead of 400 noisy findings, you get a list of two real vulnerabilities, along with a fix that is already being patched. It's a game-changer.
Kim Isenberg: Just last week, Anthropic accidentally leaked the full source code of Claude Code through an NPM package, and researchers found a vulnerability via prompt injection. What does this tell you about the expanding attack surface?
Roeland Delrue: Supply chain attacks are bleeding into the developer's machine. Hackers are using IDE extensions, GitHub actions, and AI skills to craft new worms and techniques. We actually had to start looking beyond just NPM packages—we now monitor Chrome extensions and other add-ons that developers install for potential prompt injections.
As for Anthropic leaking it... honestly, they are masters at product marketing. Every time they or OpenAI release something, they rile people up like "we've reached peak AI, it's getting dangerous!" When I heard Claude leaked, my first thought was that they might have done it on purpose to influence the narrative or the stock market. I'm still unsure if it was real or planned.
Kim Isenberg: What can AI realistically automate in security today, and where do humans need to stay in control?
Roeland Delrue: You start with the most automatable things. LLMs are great at understanding code, triaging false positives, and rewriting code to remediate vulnerabilities. But when you give agents access to terminals and browsers, they become really good at navigating—which is exactly what you need for pen testing, but also for QA testing or scraping. The humans are becoming more like orchestrators.
Kim Isenberg: How do you think the role of the developer changes over the next two years then?
Roeland Delrue: The expert developers who know how to set up and orchestrate these agents will reap the most benefits. But it also translates to non-developers. A marketing or finance person who learns to cobble these AI tools together will be the operator of the future. Just yesterday I saw a new app: it's a bot that joins your brainstorming meeting. While you and your team are discussing a new CRM app, the bot is "vibe coding" the app on the side in real-time. Software creation is becoming conversational, much like how people prefer listening to a podcast dialogue over someone reading a monologue for 10 minutes.
Kim Isenberg: Do you think we're moving toward a world where software can actually secure itself continuously, or is that still a vision?
Roeland Delrue: We're moving there. Will it mean nothing is ever hackable? No. Even Fort Knox can be broken into. Security is ultimately about economics: what resources is an attacker willing to pour in to extract something? Good security discourages the attacker and makes them move on to a weaker target. We might close the gap, but the attack surface always expands.
Kim Isenberg: Before we wrap up, is there anything else our community should know?
Roeland Delrue: There's an interesting duality happening. On one hand, there is a massive democratization of software creation—tools like Lovable turn non-developers into developers. Aikido is on a similar mission to democratize software security; we even have a direct integration with Lovable and 50,000 non-paying users on our free version. On the other hand, the world is becoming more fragmented, with a growing trend towards data sovereignty and strict control. Watching these two opposite forces—democratization versus sovereignty—will be very interesting over the next few years.
Kim Isenberg: Your philosophy of democratizing security is clearly paying off. Roeland, it was such a pleasure meeting you. All the best for the future!
Roeland Delrue: Thank you too. Bye!
Why it matters: In this interview, Aikido Security co-founder Roeland Delrue explains how the rapid rise of AI-generated "vibe coding" is accelerating software development while simultaneously creating a massive surge in security vulnerabilities. To combat this growing threat, Aikido leverages AI agents that continuously pen-test and auto-remediate codebases, paving the way for what he calls "self-securing software." Ultimately, Delrue envisions a future where these autonomous tools democratize cybersecurity, allowing developers to safely keep pace with the speed of AI.


The IT strategy every team needs for 2026
2026 will redefine IT as a strategic driver of global growth. Automation, AI-driven support, unified platforms, and zero-trust security are becoming standard, especially for distributed teams. This toolkit helps IT and HR leaders assess readiness, define goals, and build a scalable, audit-ready IT strategy for the year ahead. Learn what’s changing and how to prepare.